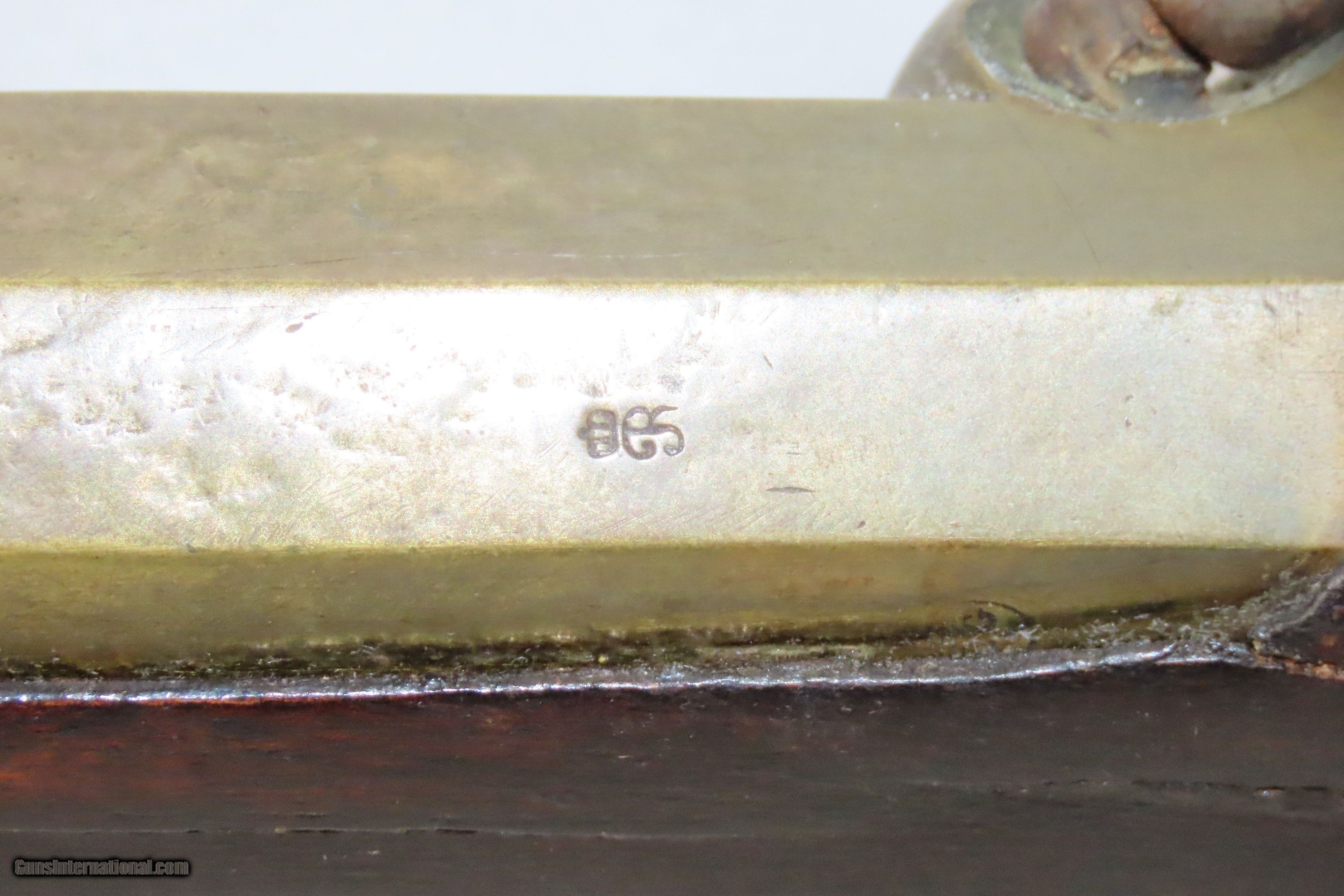
BIG BORED BELGIAN BRASS BARRELED BLUNDERBUSS Coach Gun 19th Century Antique With MM Company Inscription on the Barrel! for sale
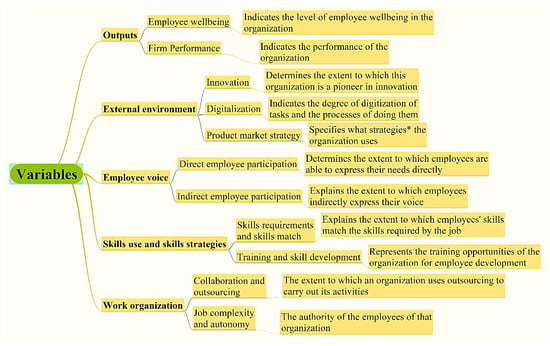
Algorithms | Free Full-Text | Correlation Analysis of Factors Affecting Firm Performance and Employees Wellbeing: Application of Advanced Machine Learning Analysis

Mozilla Foundation - State of Online Privacy Reaches 'Very Creepy' Level, Finds Mozilla's First-Annual Consumer Creep-O-Meter

OnDemand | Achieving Zero Trust – Securing Workforce and Customer Identities in a New Business ParadigmWebinar.

Background for school, school theme, school doodles, inscription in a notebook, training, lessons, time for training, Set of school tools, set of education icons, back to school Stock Vector | Adobe Stock

19 Security Awareness Statistics You Should Know Before Offering Training - Hashed Out by The SSL Store™

BIG BORED BELGIAN BRASS BARRELED BLUNDERBUSS Coach Gun 19th Century Antique With MM Company Inscription on the Barrel! for sale

BIG BORED BELGIAN BRASS BARRELED BLUNDERBUSS Coach Gun 19th Century Antique With MM Company Inscription on the Barrel! for sale